AI Writes Code.
Who Catches the Vulnerabilities?
40% of AI-generated code contains security flaws. Your AI assistant won't tell you. Git AutoReview scans every PR with 15 security rules + AI specialized security pass.
AI Code is Insecure. The Data is Clear.
Every major study reaches the same conclusion: AI-generated code introduces vulnerabilities at alarming rates.
of AI-generated programs contain vulnerabilities
NYU Copilot Study (IEEE S&P 2022)
CWE instances in 7,703 AI-generated GitHub files
CodeAnt AI 2025
more critical vulnerabilities after 5 AI iterations
Kaspersky Vibe Coding Report
higher secret leak rate in Copilot-active repos
GitGuardian Study
average data breach cost globally
IBM 2025 Report
average time to detect a breach
IBM 2025 Report
Real Security Incidents from AI-Generated Code
These happened in 2024-2025. Not hypotheticals. Not demos. Production systems, real users, real damage.
Copilot Chat prompt injection exfiltrated AWS keys from private repos via hidden PR comments. Affected ALL Copilot users. Fixed Aug 2025 after Legit Security disclosure.
CVE-2025-38561 — The Register, CSO Online
Vibe-coded startup app had zero auth. Customer credit cards accessible via URL for a week. AI never added authentication. Potential GDPR fines up to $200K.
Karo Zieminski — Substack
Amazon's AI coding tool autonomously deleted production environments, causing 13-hour outage. AI tools inherit engineer permissions without safety checks.
Tom's Hardware
1 in 5 skills in ClawHub (AI agent marketplace) were malicious. 135K exposed instances with insecure defaults. 9 CVEs, 3 with public exploits.
Antiy CERT, SecurityScorecard
Developers using AI assistants wrote less secure code in 4 out of 5 tasks while feeling MORE confident about security. AI creates a dangerous illusion of safety.
Stanford/Boneh Research
“It Won't Happen to Me”
Nobody ships a PR thinking it has a security hole in it. That's the problem — breaches take 241 days to detect precisely because the code looked fine when it merged.
AI assistants don't warn you about the vulnerabilities they introduce. The Stanford study found developers using AI felt more confident while writing less secure code.
Your code review is the last line of defense. Is it catching security issues?
Security Scanning Built Into Every Review
We added two layers of security scanning because one layer always misses something. The pattern-matching rules catch known vulnerability signatures — SQL injection, XSS, hardcoded secrets — while the AI layer traces your actual data flow to find the issues that rules-based tools are structurally blind to. It runs on every PR with zero configuration.
Layer 1: 15 Regex Rules
Fast, deterministic pattern matching runs locally in VS Code. Catches hardcoded secrets, SQL injection, eval(), XSS, weak crypto, CORS wildcards, and more. Zero false negatives for known patterns.
- Runs locally, no API call needed
- Instant results, no latency
- Severity-rated (Critical, High, Medium)
Layer 2: AI Security Pass
A specialized AI prompt focused exclusively on security. Claude, Gemini, or GPT analyzes your code changes for complex vulnerabilities that regex can't catch: logic flaws, auth bypasses, SSRF chains.
- Understands code context and intent
- Catches logic-level vulnerabilities
- BYOK — code goes direct to your AI provider
15 Built-in Security Rules
Every PR is scanned against these patterns. No configuration needed. Available on all plans including Free.
Hardcoded Secrets
API keys, passwords, tokens, private keys in source code
SQL Injection
Template literals and string concatenation in SQL queries
eval() Usage
Dynamic code execution enabling code injection attacks
Math.random for Crypto
Predictable values used where cryptographic randomness needed
innerHTML / XSS
Cross-site scripting via unsanitized HTML insertion
Weak Hashing (MD5/SHA1)
Broken cryptographic hash functions for passwords or tokens
CORS Wildcards
Permissive Access-Control-Allow-Origin allowing any domain
Empty Catch Blocks
Swallowed errors that hide security failures silently
Disabled SSL Verification
rejectUnauthorized: false or verify=False in HTTP clients
Prototype Pollution
Unsafe property assignment on Object.prototype chain
Command Injection
User input passed to shell commands or exec functions
Path Traversal
Unsanitized file paths allowing directory traversal (../)
4 Specialized AI Review Passes
Toggle each pass independently per repository. Security, Bugs, Performance, Style — enable what matters for each project.
Security
- SQL injection & NoSQL injection
- XSS & CSRF vulnerabilities
- Authentication & authorization flaws
- SSRF & path traversal
- Hardcoded secrets & credentials
- Insecure cryptography
Bugs
- Null/undefined dereferences
- Race conditions & deadlocks
- Resource leaks (memory, file handles)
- Infinite loops & recursion
- Off-by-one & boundary errors
- Unhandled promise rejections
Performance
- O(n²) nested loops
- N+1 database queries
- Memory leaks & large allocations
- Unnecessary re-renders (React)
- Missing indexes & slow queries
- Blocking I/O in async contexts
Style
- Long functions (>50 lines)
- Deep nesting (>3 levels)
- Magic numbers & strings
- SOLID principle violations
- Inconsistent naming conventions
- Dead code & unused imports
See It in Action
Security findings appear directly in your VS Code editor — pinned to the exact line, with severity scores and one-click actions.
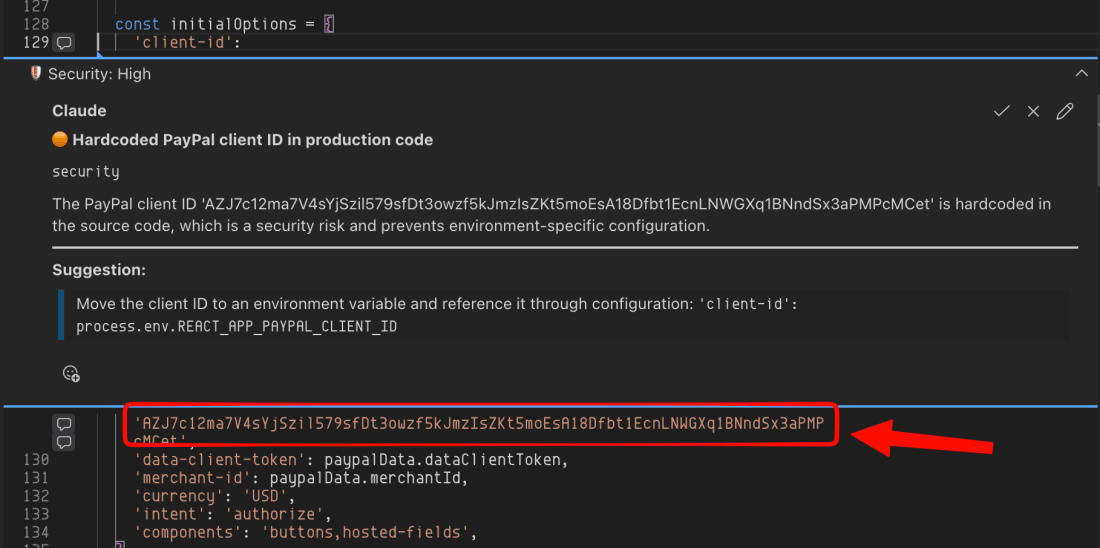
Inline Security Annotations
Security findings appear as comments pinned to the exact line — approve, reject, or navigate to the code in one click.
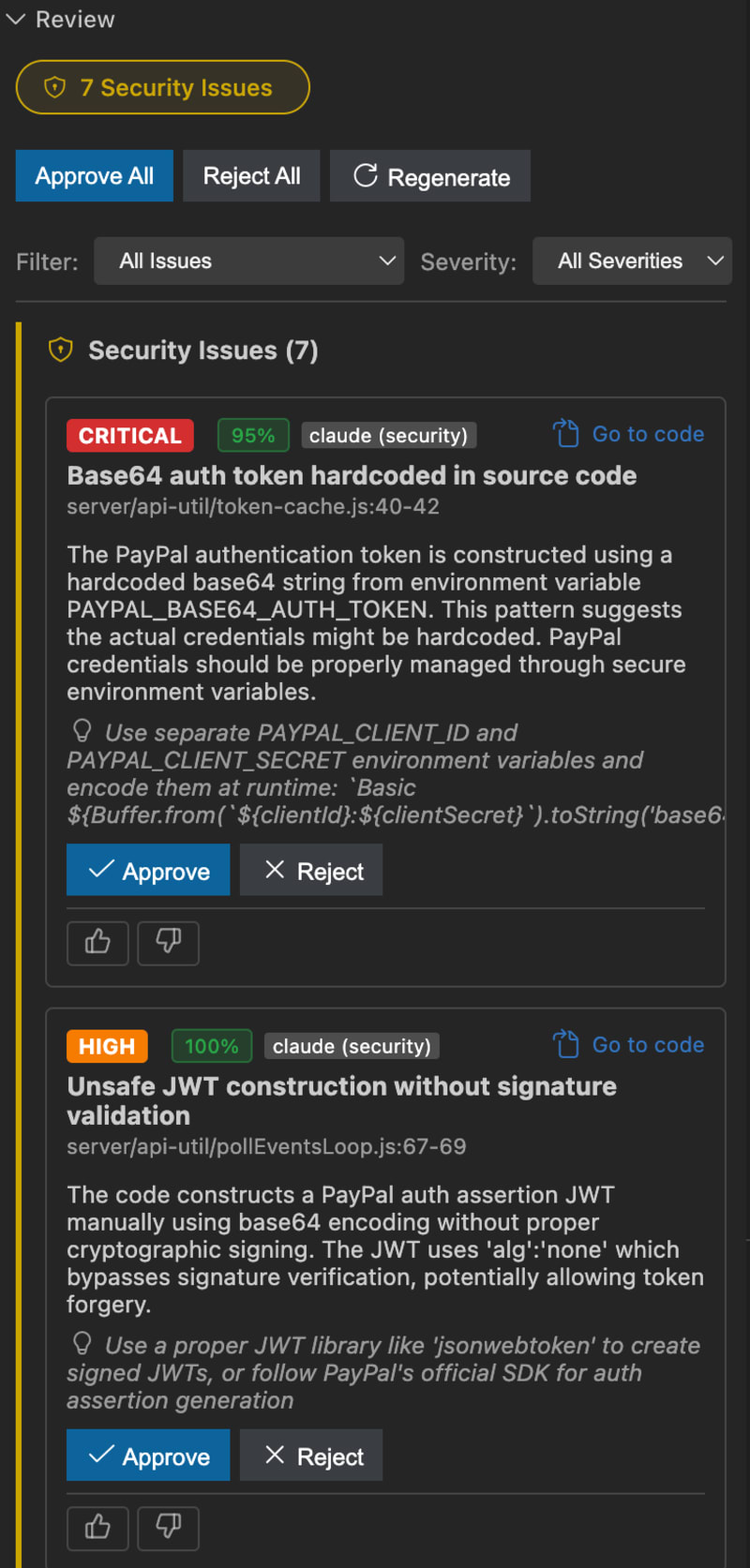
Security Scanning Results
Hardcoded secrets, SQL injection, XSS flagged with severity and confidence scores.
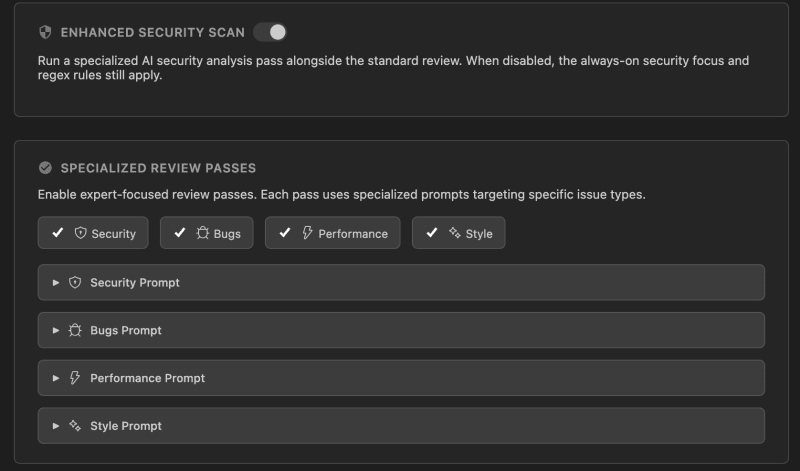
Specialized Review Passes
Four expert passes — Security, Bugs, Performance, Style — each with its own toggle.
Security Scanning: How We Compare
Git AutoReview combines AI code review with security scanning. Dedicated SAST tools have more rules; we have AI intelligence.
| Feature | Git AutoReview | CodeRabbit | Snyk | CodeQL |
|---|---|---|---|---|
| AI Code Review | 3 models (Claude, Gemini, GPT) | 1 model | No | No |
| Security Rules | 20+ regex + AI pass | Basic | 300+ rules | 2,000+ rules |
| IDE Integration | VS Code | GitHub only | VS Code, JetBrains | GitHub only |
| Human Approval | N/A | N/A | ||
| BYOK Privacy | Free (public repos) | |||
| Price | $9.99/mo | $24/user/mo | $98/mo | Free / Enterprise |
| Setup Time | 2 minutes | 10 minutes | 30 minutes | 1 hour |
| Bitbucket Support | Full (Cloud/Server/DC) | No | Limited | No |
The Cost of Inaction
Without Security Scanning
- $4.44M average breach cost
- 241 days average detection time
- Reputation damage, customer trust lost
- GDPR/regulatory fines
With Git AutoReview
- $9.99/mo Developer plan
- Instant detection during code review
- Zero code storage, BYOK privacy
- Human approval before publishing
What are vulnerability scanning tools?
Most teams discover their first serious vulnerability the hard way — a scanner fires after deployment, and suddenly a sprint gets hijacked by a triage meeting nobody planned. Tools like Nessus and QualysGuard catch network-level problems (open ports, outdated packages, misconfigurations), while Burp Suite and OWASP ZAP hammer web applications for injection flaws and broken authentication. Both categories do their job well, but they share a timing problem that frustrates developers: they find issues after code reaches a test environment, not while someone is still writing it.
Git AutoReview shifts vulnerability detection earlier. Instead of scanning a deployed application, it analyzes your pull request diff for SQL injection, XSS, hardcoded secrets, and OWASP Top 10 patterns while you review code in VS Code. This catches the same vulnerability classes that network scanners find — just weeks earlier in the development cycle, when fixes cost minutes instead of sprints.
What are SAST tools and how do they compare to AI code review?
The appeal of SAST is brute-force coverage — SonarQube ships over 6,500 rules across 30+ languages, and CodeQL traces data flow through your entire codebase with semantic queries. Snyk Code, Semgrep, Checkmarx, and Veracode each bring their own rule databases and CI/CD integrations. When a SAST scan runs, it checks everything against every rule it knows, which means zero false negatives on patterns the tool recognizes. That exhaustiveness is genuinely valuable for compliance audits and quarterly security reviews.
The trade-off is noise. Enterprise SAST deployments regularly generate hundreds of findings per scan, and teams struggle to triage them between sprint work. AI code review works differently — it reads the PR diff the way a senior engineer would, catching logic flaws, race conditions, and context-dependent bugs that no regex rule can express. The two approaches complement each other: SAST for exhaustive rule coverage, AI review for intelligent analysis of what changed.
Git AutoReview bridges the gap with 20+ built-in security rules (the SAST side) plus a specialized AI security pass that reasons about your code changes. Teams running SonarQube or Snyk for quarterly compliance audits add Git AutoReview for real-time, per-PR security feedback in VS Code — covering the gap between the last SAST scan and the next one.
What is static code analysis?
Every CI/CD pipeline already runs some form of static analysis — ESLint catches style issues, TypeScript catches type errors, and tools like Checkmarx catch security flaws. The difference between those layers matters: linters enforce conventions, type checkers prevent runtime crashes, and SAST scanners flag vulnerability patterns. Most teams stack all three without thinking about it, which is exactly the right approach because each one catches a different class of defect.
The challenge in 2026 is that AI coding assistants generate code faster than static analysis can keep up. Copilot and Cursor produce working code that passes linters and type checks while embedding subtle vulnerabilities — hardcoded tokens, missing input validation, insecure default configurations. Git AutoReview adds an AI layer on top of static analysis: it understands intent, not just syntax, and flags the security mistakes that rule-based tools miss because no one wrote a rule for that particular pattern yet.
Frequently Asked Questions
Does Git AutoReview replace Snyk or SonarQube?
What security vulnerabilities does AI code review detect?
How is this different from SAST tools?
Does it work with AI-generated code from Copilot or Cursor?
Can I customize security rules?
How does the AI security pass work?
Is my code sent to your servers for security scanning?
What platforms support security scanning?
How much does security scanning cost?
Can I toggle security scanning on or off per repository?
What are SAST tools and which ones are most popular?
What is static code analysis and when do you need it?
How do vulnerability scanning tools fit into CI/CD pipelines?
Don't Ship Vulnerable Code
Start scanning every PR for security vulnerabilities today. No credit card required. 10 free reviews per day. BYOK supported.